Cybersecurity in Manufacturing SMEs: 3 Blind Spots Revealed by Our Survey
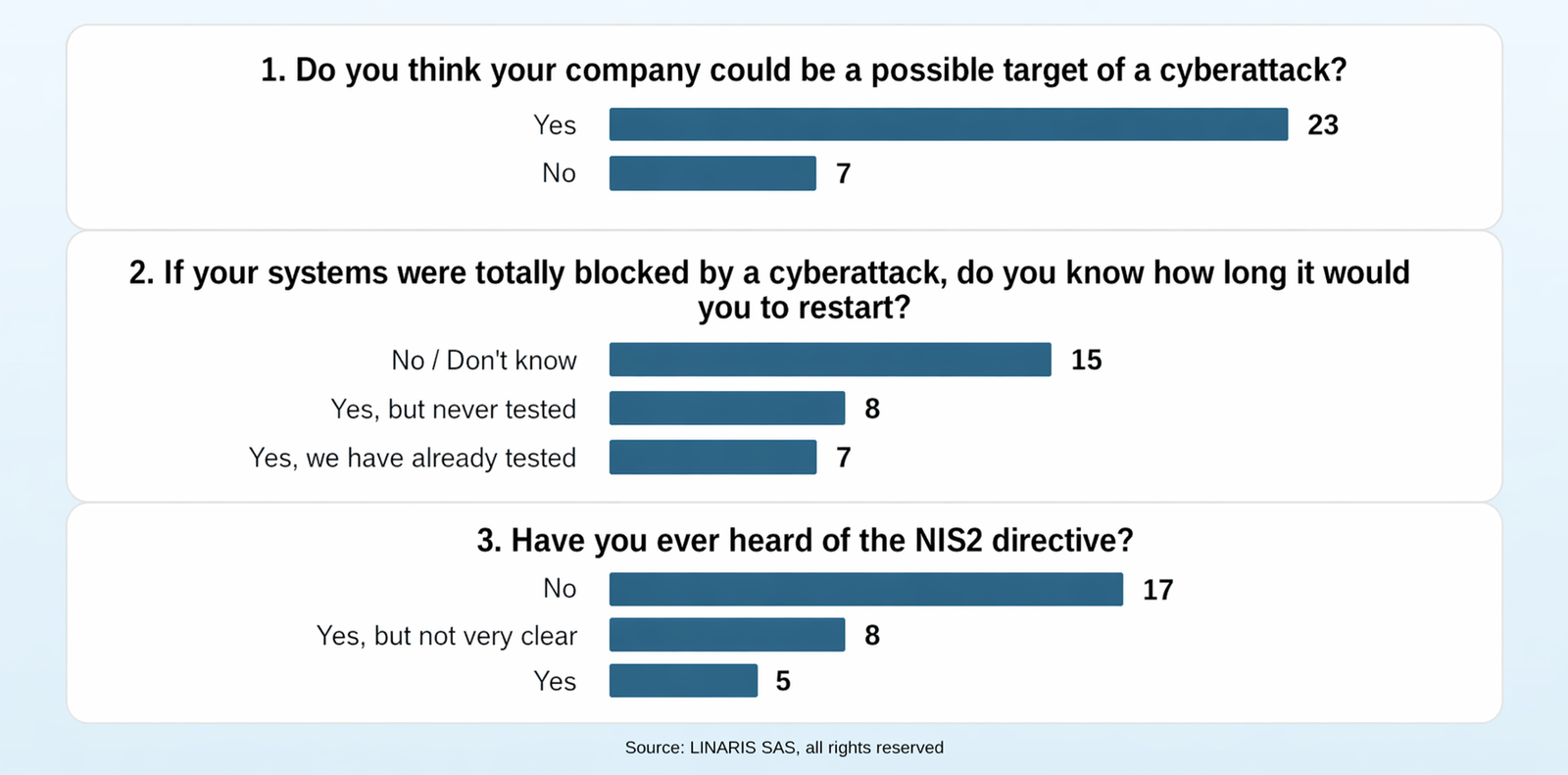
On March 30 and 31, 2026, we conducted an in-person survey of 30 French SMEs in the manufacturing sector.
Methodology note: This survey included only three questions, but it also led to direct discussions with respondents, which enriched our analysis beyond the responses alone. That said, we are fully aware that it is not intended to be statistically representative of all French manufacturing SMEs. It does, however, provide a useful field-based signal.
Our objective was to better understand how these companies perceive cyber threats, as well as their level of preparedness, so that we can adapt our awareness efforts accordingly. The context makes this necessary. Financially motivated cyberattacks are now more industrialized, more opportunistic, and affect organizations of all sizes. At the same time, the French framework for implementing the NIS2 Directive is being clarified.
Our survey highlights a clear gap between the reality of cyber threats, the level of preparedness required, and the way many SME leaders still perceive these issues.
Source : LINARIS
#1: “We are not a target”
A lingering sense of immunity
Most of the companies surveyed believe they are exposed. However, a significant proportion — 7 out of 30 — still think they cannot be a target.
The facts point in the opposite direction
Yet the latest public data shows otherwise. ANSSI (French National Cybersecurity Agency) states that SME remain among those most affected by ransomware. It also emphasizes that cybercriminals target most sectors and geographic areas. In other words, the question should no longer be, “Why us?” but rather, “What makes us easier to target?”.
Cyberattacks are becoming industrialized
This shift in thinking is all the more important because cybercrime has become increasingly professionalized.
ANSSI notably describes the ransomware-as-a-service model, which makes it possible to industrialize attacks and multiply them. In practical terms, one group provides the tools, infrastructure and sometimes even support. Affiliates then carry out the attacks in exchange for a share of the ransom payments.
We are no longer dealing with a handful of isolated hackers. We are facing a quasi-industrial model of cyberattacks. And this trend may accelerate further with generative AI, which makes campaigns faster, more credible and easier to deploy at scale.
#2: Knowing how to restart “in theory” is not enough
Recovery time is often assumed, rarely proven
Based on the responses collected, only 7 out of 30 companies appear able to say that they know their recovery time and have already tested it. But among them, some last tested it more than a year ago.
In the event of a cyberattack that brings everything to a halt — in other words, a cyber crisis — the real question is not simply whether backups exist. Above all, it is whether business activity can be restored within a timeframe that is compatible with the company’s business needs.
CNIL also points out that backup restoration, as well as the implementation of business continuity or disaster recovery plans, must be tested regularly. Until that test has taken place, this is not a proven capability, and recovery time remains an assumption.
Recovering without major loss is a leadership matter
More importantly, a recovery test is not just an IT exercise. It requires trade-offs between business priorities, decisions on what needs to be restarted first, and sometimes acceptance of a temporary degraded mode of operation. It also requires coordination across production, logistics, finance and customer relations.
IT restores systems. But only senior management can validate a recovery sequence that is aligned with the company’s business priorities.
#3: NIS2 is still unclear for many business leaders
A topic that remains little known
The level of awareness around NIS2 remains low, as 25 out of the 30 companies say they have either never heard of it or are unfamiliar with its content. This does not surprise us. It is a new, dense regulatory topic, and it is not always easy to translate into operational terms.
More than a directive, a broader signal
Yet this issue goes well beyond the circle of specialists. NIS2 is a European directive aimed at raising the level of cybersecurity across 18 critical sectors. It requires the entities concerned to strengthen the way they prevent, govern and manage cyber risk. Like the GDPR, non-compliance can lead to sanctions.
Senior management is now responsible for cybersecurity
Beyond the regulatory framework, however, the message is clear: cybersecurity is not just an IT matter; it directly involves senior management. It is an issue of governance, organization and anticipation. The European Commission also emphasizes that NIS2 strengthens top management accountability for cyber risk management.
In summary
These three findings tell the same story. Many companies have not yet fully shifted from an IT-driven view of cybersecurity to a business-driven one — that is, a view centered on business continuity, resilience and leadership responsibility.
Author
Lai LY
Cybersecurity Governance Specialist
Contributor
Stéphane HIVERT
Cybersecurity Specialist for SMEs
Thank you
We warmly thank the 30 companies in the manufacturing sector that took part in this survey for their time and for the quality of their responses.
Would you like to know where your SME stands on these three key issues — actual exposure, recovery capability, and preparedness for NIS2?
LINARIS can help.
We are one of the few consulting firms specialized in SME cybersecurity that can support you across the full cyber-resilience cycle, from assessment to governance.
Contact us for a free, no-obligation discussion.
Disclaimer
This report is provided for informational purposes only and reflects the author’s opinion at the time of analysis.
It does not constitute legal or regulatory advice and does not guarantee the absence of risks or vulnerabilities.
Threats and risk levels may evolve over time.
Any decisions taken on the basis of this report remain the sole responsibility of the reader.